You’re tired of hearing “blockchain” and “cryptography” used like they mean the same thing.
They don’t.
I’ve spent years digging into the actual code behind 50+ digital currencies. Not just skimming whitepapers, but auditing consensus logic, tracing signature schemes, and watching real attacks unfold.
Most explanations stop at the surface. They show you what a wallet is or how to buy Bitcoin. But they skip the part that actually matters: Cryptocurrencies Drhcryptology.
That’s not a typo. It’s the point.
Cryptology isn’t decoration. It’s the reason your transaction can’t be forged. The reason no one needs to trust a bank.
The reason a network stays honest even when half the nodes are lying.
You want to know how it works (not) just that it works.
So I’m cutting past the buzzwords.
No analogies. No fluff. Just clear lines between math, code, and behavior.
You’ll see exactly where cryptology holds up (and) where it breaks.
This isn’t theory. It’s what happens when real people roll out it.
And yes, I’ll show you the flaws too. Because ignoring them doesn’t make anything safer.
Let’s start with the basics (no) assumptions.
Cryptology 101: Math, Not Magic
You think cryptography is just for hackers and spies. It’s not. It’s the foundation of every digital dollar you’ve ever sent.
I learned this the hard way (debugging) a wallet that wouldn’t sign because I mixed up public and private keys. (Yes, that happened.)
Public-key crypto is simple in practice: one key signs, the other verifies. Bitcoin uses ECDSA. Solana uses Ed25519.
Same idea. Different math. Different speed.
Different trade-offs.
Hashing isn’t just for mining. It’s how your phone can verify a billion transactions without downloading them all. Merkle trees make that possible.
Light clients trust hashes (not) nodes.
Zero-knowledge proofs? Not sci-fi. Zcash runs zk-SNARKs.
But eats more CPU.
StarkNet uses zk-STARKs. One hides data well but needs trusted setup. The other doesn’t.
Think of cryptology like a legal contract system. Math replaces lawyers. Consensus replaces courts. No signatures on paper.
Just numbers that either match (or) don’t.
You’re probably wondering: Does any of this actually hold up under real load?
Yes. But only if the primitives are chosen right. And implemented without shortcuts.
That’s where Drhcryptology comes in.
It breaks down what works, what’s brittle, and what’s just marketing fluff.
Cryptocurrencies Drhcryptology isn’t a buzzword. It’s a checklist. Are you using the right hash?
The right curve? The right proof system (for) your use case?
Skip the theory. Start with the failure modes. Because when crypto fails, it fails silently.
And slowly.
Where Real-World Failures Expose Cryptological Gaps
The DAO hack in 2016 wasn’t a cryptology failure. The elliptic curve signatures held up fine. What broke was the execution layer (reentrancy,) plain and simple.
You think that’s just “smart contract logic”? So did they. Until $60 million vanished.
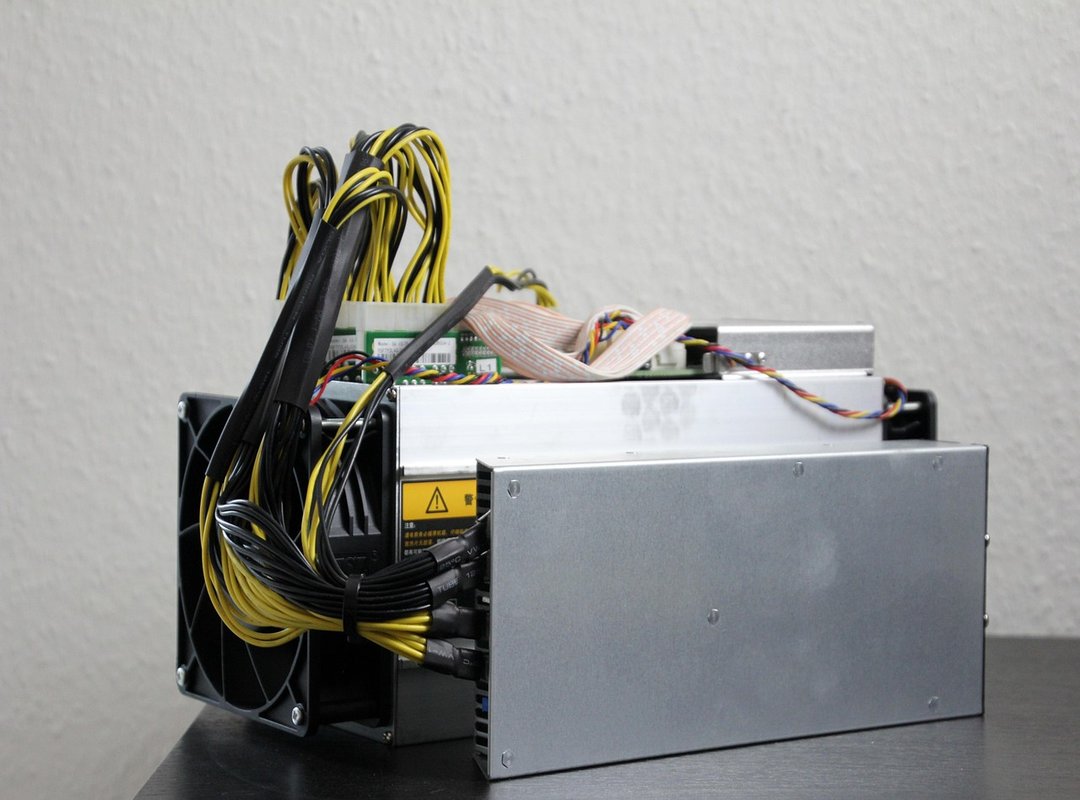
Ronin Bridge in 2022? Validators’ private keys sat on a single AWS server. No HSM.
No air gap. No rotation. The crypto itself was sound.
The key management was laughable.
Curve Finance in 2023 got hit by a Vyper compiler bug. The math didn’t lie. The compiler did.
Signature verification logic stayed intact (but) the order of checks got flipped.
Here’s what correct signature verification looks like:
if (verify(sig, msg, pubKey) && msg.isValid() && !msg.replayed)
Vulnerable version?
if (msg.isValid() && verify(sig, msg, pubKey) && !msg.replayed)
That tiny reorder let attackers bypass validation entirely.
People blame “blockchain” when the real issue is where keys live or how compilers parse code.
Misattribution isn’t harmless. It wastes time and money fixing the wrong thing.
Cryptocurrencies Drhcryptology isn’t the weak link. Humans are.
We keep pretending crypto primitives are the problem. They’re not. They’re the only part working.
Ask yourself: When your wallet asks for a seed phrase, does it tell you how it’s stored? Or just say “secure”?
Spoiler: Most don’t.
Pro tip: If a tool won’t show you its key derivation path in plain text, walk away.
The cryptography is fine. The rest? That’s where you get burned.
Post-Quantum Crypto Isn’t Waiting for Quantum Computers
I watched a dev team rebuild their wallet’s signing layer twice last year. Not because of bugs. Because they ignored NIST’s PQC timeline.
NIST finalized Kyber and Dilithium in 2024. That’s not a heads-up. That’s the starting gun.
You think your Bitcoin stash is safe because it’s “offline”? Try explaining that to a quantum computer with enough qubits. And enough time.
To crack ECDSA keys reused across years of transactions.
Lattice-based schemes like CRYSTALS-Kyber shrink key sizes but demand more CPU on verification. XMSS signatures? Huge.
Like, 10x bigger than ECDSA. That kills UTXO efficiency fast.
Account-model chains handle this slightly better. But “slightly” doesn’t help if your smart contract uses one key for ten years.
IOTA’s Qubic testnet runs Kyber now. Ethereum’s research group dropped Dilithium PoCs last quarter. Algorand’s PQ-ready key rotation proposal?
It assumes you’re rotating keys every 90 days. Not optional. Required.
That’s why “future-proofing” is nonsense. Quantum resistance changes how you hold assets today. Reuse a key?
You’re betting your cold storage stays cold forever.
And if you’re trading on Binance, you should know how they’re handling this shift (check) the this post breakdown.
Cryptocurrencies Drhcryptology isn’t academic. It’s operational.
Your node. Your wallet. Your backup phrase.
All need new assumptions.
I stopped using deterministic key derivation for long-term custody six months ago.
You should too.
Cryptographic Audit: 5 Things I Check First
I open the GitHub repo. I skim the RFC-style docs. I ask: Is this crypto actually auditable?
(1) Signature scheme transparency
Red flag: “Proprietary signature algorithm. Details under NDA.”
Green flag: Public spec + third-party audit report linked in README.
(2) Hash function collision resistance
SHA-256? Fine. SHA-1?
Walk away. If they’re still using MD5 for anything, close the tab. (Yes, someone did.)
(3) Randomness source quality
RFC 9381 compliance isn’t optional.
No entropy spec? Assume it’s /dev/random on a toaster.
(4) Side-channel resistance claims
Timing leaks break ECDSA. Power analysis breaks everything. No test evidence?
Then it’s not resistant. It’s hoped to be.
(5) Upgrade path for cryptographic agility
Can they swap SHA-256 for SHA-3 without a hard fork?
If transaction structures hardcode algorithms, they can’t.
This isn’t theoretical. You can run this checklist in under 10 minutes. Just read their docs.
Click their links. Ask if you’d trust your keys to it.
Cryptocurrencies Drhcryptology means nothing if the crypto isn’t tested, not just named.
For deeper dives into real-world trade-offs, see our Cryptocurrency Advice Drhcryptology guide.
Math Doesn’t Lie. Promises Do.
I’ve shown you the core truth: digital currencies live or die by their cryptological guarantees. Not by price charts or influencer tweets.
You now know how to spot real infrastructure versus shiny vapor.
That’s why Cryptocurrencies Drhcryptology matters. It’s not theory. It’s your filter.
So pick one digital currency you actually use (or) one you keep checking the price of.
Find its official cryptographic specification document. (Yes, it exists.)
Run it through the 5-point audit checklist. Right now.
If you skip this, you’re trusting luck instead of math.
And luck doesn’t sign transactions.
If you can’t verify the math, you’re not holding a digital currency (you’re) holding a promise.

 Head of Research & Blockchain Insights
Head of Research & Blockchain Insights
